DongleSpy v1.0 by Independent (IND)
1 of 46 files
independent
windows
-
This download is a Windows program, but it should only be run on your computer if you trust it.
Instead, run it isolated in Windows Sandbox, VirtualBox or Parallels.
Browsers may flag this download as unwanted or malicious. If unsure, scan it with VirusTotal. -
Last modified Jun 29, 2003 5:27:06 PM
MD5 checksum a9a580d08841b5636795b8b51cf3d0c1
Mime type Zip archive data
Download dongspy.zip
Size 27 kB
1996 July 4
- Zip - Windows / Computer tool
- The Slavic, program credits
4 items in the archive
- RNBOSPY.DLL
- readme.txt
- dongspy.exe
- file_id.diz
DongleSpy v1.0
by The Slavic
This program was designed to deal with Rainbow Technologies
SentinelSuperPro hardware key protected Windows NT/ Windows95 applications.
In particular it will work only with apps that use dynamic linked Sentinel's
libraries (DLLs). Once it is started, the program intercepts dongle <-> app-
lication data exchange and after converting it to the human-readable format
stores it in the *.out log file. Because of the necessity to work around
Windows NT/95 security, the program turned out to be rather complicated.
You can figure out how it works spending some time fishing around in the
currently available books or in the MSDN libraries.
The usage of the program is very simple. Just make sure rnbospy.dll
and dongspy.exe files are in the same directory. Start dongspy.exe and
type in the full path and the file name of the dongle-protected application
and Sentinel's DLL (you can use a built-in browser). The default name of
the DLL is sx32w.dll, but it could have any name. Make sure you specify the
right DLL, otherwise it's not going to work!
In the next version I'll include auto-search but for right now it's your
job to find the DLL. But that's about it. Just press `RUN' and work with
your application as you would do without the spying utility. There's a very
small overhead, mostly due to the writing to the log file. Probably you wont
even notice the difference in speed. After you exit the application, you'll
see the new file with the same name as the name of your application and
extension `out'. It is the ascii log file which you can open with any text
editor and examine the information. Generally, the longer you run the
application, the more data you get. This version of the utility works in a
passive mode: it's waiting for the application to request the data from the
dongle. Because of this, you may not get all the data cells that are used by
the application. The next version (if will ever be finished) will pull out
the data from ALL available data cells before the application exits, which
will guarantee 100% success for emulating the sentinel dongles that use only
the data cells. It's not likely that the program will try to overwrite the
data (or algorithm) cells because of the limited number of overwrites
allowed for a given cell ( the physical limit is about 100000). But even in
case it happens, it doesn't seem to be a big deal to keep track of all the
overwrites. In addition, if the protection scheme attempts to overwrite data
or algorithm cells, the spy utility will intercept the `write' and two
`overwrite' passwords! The more complicated case is the algorithm cells.
They cannot be read even by developers. The only thing we can do right now is
to intercept and log all the Queries and dongle's answers. All the algorithm
activate passwords will also be logged (if used). The Increments and
Decrements of the Counter cell (i.e. could be used in demo versions to keep
track of the number of times the application was executed, etc..) will be
logged as well. The `return address' that will be found in the log file after
every API call, indicates the address where API function will return control
after it's done. If the application doesn't do any tricks, that address could
be pretty useful for finding the place in the code where the call was
originated from.
Well. that's about it. At the end of this file you'll find an
example of the output you can expect to see after running the application.
It's a part of the real log file that was created when I tested the utility
on the Rainbow's test program that is available from Rainbow Technologies's
web site (www.rnbo.com). The spy utility will intercept ALL the documented
API calls (only part of them is shown on the sample output). Have fun...
The Slavic
04.07.96
SentinelSuperPro(tm) is a trade mark of Rainbow Technologies, Inc. Microsoft
Windows(tm), Microsoft Windows NT(tm), Microsoft Windows 95(tm) are
trademarks of Microsoft Corp. All other product names referenced herein are
trademarks or registered trademarks of their respective manufactures.
**************************************************************
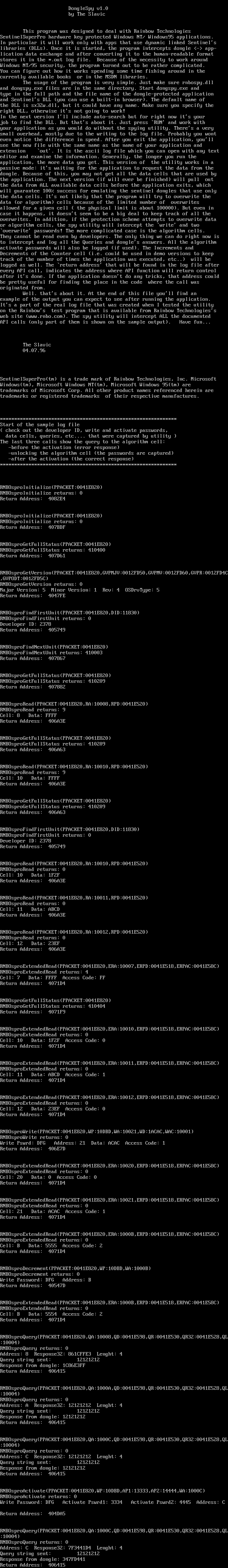
Start of the sample log file
( check out the developer ID, write and activate passwords,
data cells, queries, etc.... that were captured by utility )
The last three calls show the query to the algorithm cell:
-before the activation (error response)
-unlocking the algorithm cell (the passwords are captured)
-after the activation (the correct response)
**************************************************************
RNBOsproInitialize(PPACKET:0041E820)
RNBOsproInitialize returns: 0
Return Address: 4082E4
RNBOsproInitialize(PPACKET:0041E820)
RNBOsproInitialize returns: 0
Return Address: 407BDF
RNBOsproGetFullStatus(PPACKET:0041E820)
RNBOsproGetFullStatus returns: 410400
Return Address: 407D61
RNBOsproGetVersion(PPACKET:0041E820,GVPMJV:0012FD50,GVPMV:0012FD60,GVPR:0012FD4C,GVPODT:0012FD5C)
RNBOsproGetVersion returns: 0
Major Version: 5 Minor Version: 1 Rev: 4 OSDrvType: 5
Return Address: 4047FE
RNBOsproFindFirstUnit(PPACKET:0041E820,DID:11830)
RNBOsproFindFirstUnit returns: 0
Developer ID: 2378
Return Address: 405749
RNBOsproFindNextUnit(PPACKET:0041E820)
RNBOsproFindNextUnit returns: 410003
Return Address: 407867
RNBOsproGetFullStatus(PPACKET:0041E820)
RNBOsproGetFullStatus returns: 410209
Return Address: 407882
RNBOsproRead(PPACKET:0041E820,RA:10008,RPD:0041E520)
RNBOsproRead returns: 9
Cell: 8 Data: FFFF
Return Address: 406A3E
RNBOsproGetFullStatus(PPACKET:0041E820)
RNBOsproGetFullStatus returns: 410209
Return Address: 406A63
RNBOsproRead(PPACKET:0041E820,RA:10010,RPD:0041E520)
RNBOsproRead returns: 9
Cell: 10 Data: FFFF
Return Address: 406A3E
RNBOsproGetFullStatus(PPACKET:0041E820)
RNBOsproGetFullStatus returns: 410209
Return Address: 406A63
RNBOsproFindFirstUnit(PPACKET:0041E820,DID:11830)
RNBOsproFindFirstUnit returns: 0
Developer ID: 2378
Return Address: 405749
RNBOsproRead(PPACKET:0041E820,RA:10010,RPD:0041E520)
RNBOsproRead returns: 0
Cell: 10 Data: 1F2F
Return Address: 406A3E
RNBOsproRead(PPACKET:0041E820,RA:10011,RPD:0041E520)
RNBOsproRead returns: 0
Cell: 11 Data: ABCD
Return Address: 406A3E
RNBOsproRead(PPACKET:0041E820,RA:10012,RPD:0041E520)
RNBOsproRead returns: 0
Cell: 12 Data: 23EF
Return Address: 406A3E
RNBOsproExtendedRead(PPACKET:0041E820,ERA:10007,ERPD:0041E518,ERPAC:0041E58C)
RNBOsproExtendedRead returns: 4
Cell: 7 Data: FFFF Access Code: FF
Return Address: 4071D4
RNBOsproGetFullStatus(PPACKET:0041E820)
RNBOsproGetFullStatus returns: 410404
Return Address: 4071F9
RNBOsproExtendedRead(PPACKET:0041E820,ERA:10010,ERPD:0041E518,ERPAC:0041E58C)
RNBOsproExtendedRead returns: 0
Cell: 10 Data: 1F2F Access Code: 0
Return Address: 4071D4
RNBOsproExtendedRead(PPACKET:0041E820,ERA:10011,ERPD:0041E518,ERPAC:0041E58C)
RNBOsproExtendedRead returns: 0
Cell: 11 Data: ABCD Access Code: 1
Return Address: 4071D4
RNBOsproExtendedRead(PPACKET:0041E820,ERA:10012,ERPD:0041E518,ERPAC:0041E58C)
RNBOsproExtendedRead returns: 0
Cell: 12 Data: 23EF Access Code: 0
Return Address: 4071D4
RNBOsproWrite(PPACKET:0041E820,WP:10DBD,WA:10021,WD:1ACAC,WAC:10001)
RNBOsproWrite returns: 0
Write Pswrd: DFG Address: 21 Data: ACAC Access Code: 1
Return Address: 406E7D
RNBOsproExtendedRead(PPACKET:0041E820,ERA:10020,ERPD:0041E518,ERPAC:0041E58C)
RNBOsproExtendedRead returns: 0
Cell: 20 Data: 0 Access Code: 0
Return Address: 4071D4
RNBOsproExtendedRead(PPACKET:0041E820,ERA:10021,ERPD:0041E518,ERPAC:0041E58C)
RNBOsproExtendedRead returns: 0
Cell: 21 Data: ACAC Access Code: 1
Return Address: 4071D4
RNBOsproExtendedRead(PPACKET:0041E820,ERA:1000B,ERPD:0041E518,ERPAC:0041E58C)
RNBOsproExtendedRead returns: 0
Cell: B Data: 5555 Access Code: 2
Return Address: 4071D4
RNBOsproDecrement(PPACKET:0041E820,WP:10DBD,WA:1000B)
RNBOsproDecrement returns: 0
Write Password: DFG Address: B
Return Address: 40547D
RNBOsproExtendedRead(PPACKET:0041E820,ERA:1000B,ERPD:0041E518,ERPAC:0041E58C)
RNBOsproExtendedRead returns: 0
Cell: B Data: 5554 Access Code: 2
Return Address: 4071D4
RNBOsproQuery(PPACKET:0041E820,QA:10008,QD:0041E598,QR:0041E530,QR32:0041E528,QL:10004)
RNBOsproQuery returns: 0
Address: 8 Response32: 861CFFE3 Lenght: 4
Query string sent: 12121212
Response from dongle: 1C86E3FF
Return Address: 406415
RNBOsproQuery(PPACKET:0041E820,QA:1000A,QD:0041E598,QR:0041E530,QR32:0041E528,QL:10004)
RNBOsproQuery returns: 0
Address: A Response32: 12121212 Lenght: 4
Query string sent: 12121212
Response from dongle: 12121212
Return Address: 406415
RNBOsproQuery(PPACKET:0041E820,QA:1000C,QD:0041E598,QR:0041E530,QR32:0041E528,QL:10004)
RNBOsproQuery returns: 0
Address: C Response32: 12121212 Lenght: 4
Query string sent: 12121212
Response from dongle: 12121212
Return Address: 406415
RNBOsproActivate(PPACKET:0041E820,WP:10DBD,AP1:13333,AP2:14444,WA:1000C)
RNBOsproActivate returns: 0
Write Password: DFG Activate Pswrd1: 3334 Activate Pswrd2: 4445 Address: C
Return Address: 404DA5
RNBOsproQuery(PPACKET:0041E820,QA:1000C,QD:0041E598,QR:0041E530,QR32:0041E528,QL:10004)
RNBOsproQuery returns: 0
Address: C Response32: 7F3441D4 Lenght: 4
Query string sent: 12121212
Response from dongle: 347FD441
Return Address: 406415